Securing OpenClaw with Timeplus: A Real-Time Defense Architecture
- Gang Tao

- Mar 20
- 8 min read
OpenClaw is one of the most popular open-source AI agent frameworks in history, with 214,000+ GitHub stars. It is also one of the most vulnerable:
9+ | disclosed CVEs (including CVSS 9.8 pre-auth RCE) |
220,000+ | publicly exposed instances |
15,200+ | vulnerable unique IPs (critical RCE exposure) |
Up to 20% | of community packages are confirmed malware, in skill registry |
This is a massive public attack surface. With these vulnerabilities, enterprises face extraordinary risk deploying it without purpose-built security monitoring.
In this blog, we'll break down OpenClaw's security architecture and known vulnerabilities, and share a concrete implementation plan using Timeplus' streaming SQL engine as a real-time security backbone. This will process millions of agent events per second with 4ms end-to-end latency to detect prompt injection, data exfiltration, privilege escalation, and supply chain attacks as they happen.

The AI agent threat landscape evolved dramatically in late 2025 and early 2026. OWASP published both its LLM Top 10 (2025) and a new Agentic Applications Top 10 (December 2025). NIST launched its AI Agent Standards Initiative in February 2026. Meanwhile, critical vulnerabilities hit every major framework—Langflow suffered CVSS 9.8 RCE exploited in the wild, MCP servers had 43% command injection rates, and OpenClaw became what Palo Alto Networks called "potentially the biggest insider threat of 2026." The combination of Timeplus's streaming analytics with structured agent telemetry offers enterprises a viable path to deploy AI agents with continuous, real-time security oversight.
OpenClaw's architecture creates a uniquely broad attack surface
OpenClaw is a TypeScript-based gateway daemon that connects 20+ messaging platforms (WhatsApp, Slack, Telegram, Discord, Teams, Signal, iMessage) to LLM-powered agents. Created by Peter Steinberger and launched in November 2025 as "Clawdbot," it was renamed twice before settling on OpenClaw in January 2026. Its architecture has four core components relevant to security analysis:
The Gateway runs as a persistent daemon on WebSocket ws://127.0.0.1:18789, routing messages, maintaining sessions, and managing tools.
The Agent Loop follows a cycle: input → context assembly (system instructions + conversation history + tool schemas + skills + memory) → model inference → tool execution → repeat → reply.
Memory is stored as plain Markdown and YAML files under ~/.openclaw/, with MEMORY.md for persistent memory and HEARTBEAT.md for scheduled tasks.
The Skills system uses modular capability packs stored as directories containing SKILL.md files with metadata, instructions, and executable code—installable from the public ClawHub registry.
The framework supports arbitrary shell command execution, filesystem read/write, browser automation via Chrome DevTools Protocol, and cron scheduling. It is model-agnostic, supporting Claude, GPT, Gemini, DeepSeek, and local models via Ollama. This breadth of capability is precisely what makes it dangerous: Simon Willison's "lethal trifecta" of access to private data, exposure to untrusted content, and ability to communicate externally is present by design.
Ten critical weaknesses that demand monitoring:
Despite these features, OpenClaw's security posture has fundamental gaps that make real-time monitoring essential rather than optional:
Authentication disabled by default—the gateway ships unauthenticated; connections from localhost get full access
No input sanitization—web pages, emails, and documents enter the LLM context window without filtering
Skills execute untrusted code with full local access from a minimally moderated public registry
Plaintext credential and conversation storage with no encryption at rest
WebSocket security failures—no origin validation, enabling cross-site hijacking (ClawJacked vulnerability)
No sandboxing by default—tools invoked from group chats access environment variables, API keys, and filesystems
Prompt injection explicitly declared out of scope in SECURITY.md unless it includes a boundary bypass
93% of exposed instances exhibited authentication bypass due to default configurations
Shared session dangers—default dmScope=main means secrets loaded for one user become visible to others
No bug bounty program and limited dedicated security team resources
Microsoft's assessment is unambiguous:
"OpenClaw should be treated as untrusted code execution with persistent credentials. It is not appropriate to run on a standard personal or enterprise workstation."
Between January and March 2026, OpenClaw disclosed 9+ CVEs across three patch cycles, revealing the severity of its security challenges. The most critical vulnerabilities tell a story of architectural weaknesses being discovered faster than they can be fixed.
The ClawJacked vulnerability, discovered by Oasis Security in February 2026, demonstrated that malicious websites could hijack local OpenClaw agents via WebSocket even when password-protected.
Furthermore, with the only requirement to publish a skill being a GitHub account at least one week old, it’s not a surprise that 900 skills (~20% of the ecosystem) are malicious, based on Bitdefender’s estimate.
Enter Timeplus: Real-time context & detection foundation for agent security
Timeplus is a unified streaming and historical data processing platform built in C++, designed for real-time analytics with sub-second latency. Its open-source core, Proton, runs as a single binary under 500MB with no external dependencies. Timeplus Enterprise adds multi-node clustering, 200+ connectors, RBAC, alerting, and dashboards.
The architecture has three layers critical to understanding its security monitoring capability. NativeLog is an append-only, high-throughput write-ahead log optimized for low-latency writes, similar to Kafka's commit log. The Historical Store is built on ClickHouse's storage engine, supporting both columnar and row-based formats. The Unified Query Engine uses vectorized SIMD operations and JIT compilation to intelligently route queries to either layer, eliminating the need for separate real-time and batch pipelines.
Performance benchmarks demonstrate 90 million events per second on an Apple M2 Max, 4ms end-to-end latency, and 1M+ messages/second for security correlation rules on a single machine. This performance is critical for agent security monitoring, where detection latency directly determines the window of exploitation.
Streaming SQL as a security detection language
Timeplus's default query mode is streaming—SELECT ... FROM stream continuously processes future events. This fundamental design choice makes it naturally suited to security monitoring.
Three window types enable different detection patterns:
Tumble windows (fixed, non-overlapping) suit periodic aggregation: counting failed authentication attempts per 5-minute interval, calculating error rates per minute, or summarizing token consumption per hour.
Hop windows (sliding, overlapping) enable continuous threshold monitoring: detecting IP addresses making excessive requests in rolling 1-minute windows updated every second.
Session windows (dynamic, activity-based) track user or agent sessions, closing after configurable idle periods—ideal for detecting anomalous session durations or multi-step attack sequences.
Materialized views run continuously and persist results, enabling behavioral baselines against which anomalies can be measured. Complex Event Processing via JavaScript and Python UDFs allows pattern matching beyond what SQL alone can express, including finite state machines for multi-step attack detection. Python UDFs can embed ML models (scikit-learn, PyCaret) or call external LLM APIs for zero-shot anomaly classification directly within the streaming pipeline.
The built-in alerting system (Timeplus 3.0) supports batch event aggregation, throttling, and suppression to prevent alert fatigue, with actions routing to Slack, PagerDuty, webhooks, or custom Python functions.
Reference architecture for monitoring OpenClaw with Timeplus
The integration architecture follows an event-driven pattern with four layers: instrumentation, transport, detection, and response.
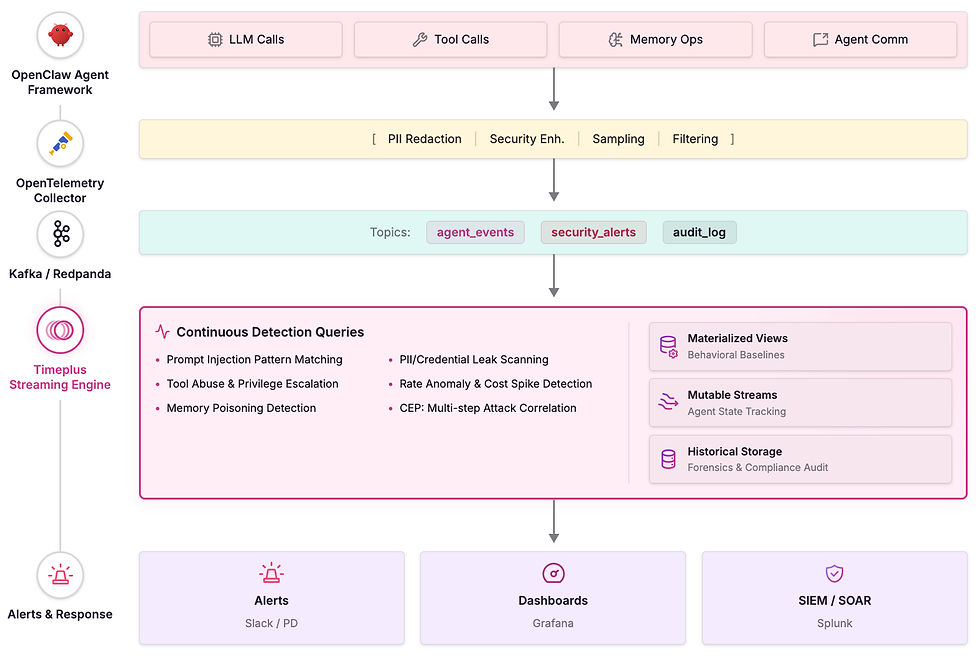
The Kafka layer is optional here, As Timeplus natively supports OpenTelemetry ingestion — no Kafka or intermediate message broker is required if users want to directly send those metrics and logs to Timeplus. Timeplus's OTel Input emulates standard OTLP HTTP and gRPC endpoints (/v1/logs, /v1/metrics, /v1/traces), meaning OpenClaw's built-in diagnostics-otel plugin (or any OTel Collector) can send telemetry directly to Timeplus by simply pointing to its IP and port. This eliminates an entire infrastructure layer, reducing deployment complexity, operational overhead, and end-to-end latency.
Setting up Timeplus OTel Input
Timeplus's OTel Input is created with a single SQL statement. First, create the target streams with Timeplus's predefined OTel-compatible schemas (which include bloom filter indexes on all attribute maps for efficient querying), then wire them to the input:
The predefined trace stream schema natively stores all OTel GenAI semantic convention attributes in span_attributes as map(low_cardinality(string), string), which means attributes like gen_ai.request.model, gen_ai.usage.input_tokens, gen_ai.tool.name, and gen_ai.agent.id are automatically captured and queryable without any schema transformation.
Two deployment patterns
Direct mode (simple deployments): Configure OpenClaw's diagnostics-otel plugin to send OTLP directly to Timeplus's OTel Input endpoint. This is the simplest setup — zero additional infrastructure:
{
"diagnostics": {
"enabled": true,
"otel": {
"enabled": true,
"endpoint": "http://timeplus-host:4317",
"protocol": "grpc",
"traces": true, "metrics": true, "logs": true
}
}
}Collector mode (enterprise deployments): Interpose an OTel Collector between OpenClaw and Timeplus for PII redaction, sampling, enrichment, and multi-destination fan-out. The Collector simply uses Timeplus as an OTLP endpoint:
# OTel Collector config — Timeplus is just another OTLP endpoint
exporters:
otlphttp/timeplus:
endpoint: http://timeplus-host:4317
compression: gzip
otlphttp/siem:
endpoint: http://splunk-otel:4318
service:
pipelines:
traces:
receivers: [otlp]
processors: [memory_limiter, batch, transform/pii_redaction]
exporters: [otlphttp/timeplus, otlphttp/siem]Streaming SQL detection queries for every major threat
Because Timeplus stores OTel traces with GenAI semantic convention attributes in span_attributes maps, security detection queries access these attributes directly using map access syntax.
Prompt injection detection in real time
Prompt injection is the #1 threat to AI agents and OpenClaw's most fundamental weakness. Detection requires layered approaches: pattern matching for known injection phrases, statistical anomaly detection for behavioral deviations, and ML-based classification for novel attacks.
For OpenClaw's specific indirect injection vectors (malicious emails, web scraping, skill content), a Python UDF can score content using a lightweight classifier:
Data exfiltration monitoring
OpenClaw's demonstrated vulnerability to credential leakage and data exfiltration through agent outputs requires continuous scanning of all output content.
Privilege escalation and tool misuse detection
OpenClaw's shell execution, filesystem access, and browser automation tools represent high-risk capabilities that require granular monitoring.
Behavioral baseline and anomaly detection
Materialized views establish normal patterns against which deviations trigger alerts—essential for detecting novel attacks that don't match known signatures.
Memory poisoning and supply chain attack detection
Given ClawHub's documented supply chain compromise, monitoring skill installations and memory operations is critical.
Multi-step attack correlation via session windows
Session windows in Timeplus naturally group related events, enabling detection of multi-step attack sequences like probe → injection → exfiltration.
Compliance architecture meets regulatory requirements
The EU AI Act (enforcement 2025–2026) requires high-risk AI systems to maintain automatic event logs recording timestamps, reference datasets, input data, and identity of persons involved. NIST's AI Risk Management Framework mandates decision-level logging, justification tracking, and threat modeling for semantic attack vectors. ISO/IEC 42001 requires risk assessments for input manipulation and unauthorized modifications.
Timeplus's audit logging stream captures all required fields:
Tiered storage policies in Timeplus Enterprise route hot data to local NVMe SSDs and cold data to S3, with configurable TTL per stream. For compliance requiring multi-year retention, Apache Iceberg integration provides long-term lakehouse storage with full query capability.
Conclusion
OpenClaw's combination of massive adoption, architectural security gaps, and a compromised supply chain creates an environment where real-time security monitoring is not optional—it is a prerequisite for any enterprise deployment. The framework's explicit exclusion of prompt injection from its security scope, authentication-off defaults, and plaintext credential storage mean that security must be enforced externally.
Timeplus's streaming SQL engine provides the technical foundation to close this gap. Its 4ms detection latency, native tumble/hop/session windows, materialized view baselines, and CEP capabilities via UDFs align precisely with the detection requirements for every OWASP Agentic Top 10 threat category. The architecture described here—OTel instrumentation → Kafka transport → Timeplus detection → Grafana visualization + SIEM integration—represents a production-ready pattern that scales from single-instance deployments to enterprise fleets.
Three insights emerge from this analysis that go beyond conventional wisdom:
First, supply chain monitoring matters more than prompt injection defense for OpenClaw specifically—the ClawHub compromise effected 12–20% of the entire ecosystem, a vector that pattern-based prompt injection detection alone would miss. Monitoring skill installations and validating against approved lists is the highest-ROI detection to deploy first.
Second, behavioral baselines are more valuable than signature matching because the agent threat landscape evolves faster than rule databases can be updated. Materialized views tracking normal tool usage, token consumption, and session patterns catch novel attacks that keyword matching cannot.
Third, the compliance case is as strong as the security case—EU AI Act Article 12 requirements for automatic event logging, combined with NIST's AI Agent Standards Initiative, mean that enterprises will need this monitoring infrastructure regardless of their threat model, making early investment in Timeplus-based observability a dual-purpose asset for both security and regulatory readiness.
Ready to try Timeplus? Download a 30-day free trial, risk-free. See installation options here: timeplus.com/download.
